In today's virtual age, your digital identity is more critical than ever before. Unfortunately, cybercriminals are constantly looking for new ways to acquire personal details. To defend yourself from fraudulent activity, it's essential to take steps to strengthen your digital footprint.
- Develop complex passwords and ever reuse them across separate accounts.
- Stay vigilant of scam emails that ask for personal details.
- Monitor your credit card activity regularly for suspicious occurrences.
With adopting these fundamental measures, you can significantly lower your vulnerability to online fraud.
Navigating the Complexities of copyright Laws and Regulations
The realm of fake identification exhibits a labyrinthine landscape of stringent laws and regulations. Crafting and manipulating these illicit documents often carries harsh penalties, ranging from hefty penalties to imprisonment. Understanding the nuanced aspects of these legal frameworks is crucial for anyone considering to interpret this precarious terrain.
- Furthermore, awareness of the evolving nature of copyright legislation is indispensable. Law enforcement constantly introduce modified strategies to thwart the production and use of copyright identification.
- ,Therefore, staying abreast of these legal developments is crucial for citizens to evade legal ramifications.
The Rise of Biometrics: A New Era in Identity Verification
As technology continues to evolve at a rapid pace, the requirement for robust and reliable identity verification methods has never been greater. Classic methods such as passwords and PINs are increasingly vulnerable to breaches, making them inadequate for safeguarding sensitive information in today's interconnected world. This is where biometrics enters the equation. Biometrics, the science of measuring unique biological traits, offers a powerful and reliable solution for verifying identities.
Applications of biometrics are widespread across various sectors, from commerce and patient care to government. Fingerprint scanning, facial recognition, iris identification, and voice authentication are just a few examples of the varied biometric technologies being implemented today.
With its ability to provide reliable identification based on inherent physiological characteristics, biometrics offers several benefits over traditional methods. It is highly secure to forgery and tampering, as it leverages unique biological traits that are difficult to replicate. Moreover, biometrics can be integrated seamlessly into existing platforms, making it a adaptable solution for businesses of all sizes.
Countering Identity Theft with Advanced Verification Technologies
In today's increasingly digital world, identity theft poses a significant threat to individuals and organizations. To combat this escalating problem, advanced verification technologies are emerging as essential tools for protecting sensitive information. These technologies utilize sophisticated algorithms and analytics to authenticate user identities with greater accuracy and dependability.
- Facial recognition systems provide a highly secure means of verifying users based on their unique biological traits.
- Multi-factor authentication adds an extra layer of safeguarding by requiring users to provide multiple forms of verification.
- Pattern analysis monitors user actions to detect anomalies that may indicate illegitimate activity.
By implementing these advanced verification technologies, organizations can minimize the risk of identity theft and protect their customers' assets. It is essential for businesses to remain updated of Cybersecurity and fake IDs the latest advancements in this field and adopt robust verification solutions to ensure the security of their systems and customers.
Protecting Your Personal Data: Best Practices for Identity Security
In today's digital landscape, safeguarding your personal information is paramount. cybersecurity threats are ever-present, making it crucial to implement robust practices to protect your identity. One of the most important steps is to utilize strong and unique passwords for all your online accounts. Avoid duplicating passwords across different platforms, as this exposes you to security breaches. Furthermore, be wary of phishing attempts and dangerous links in emails or messages. Always verify the sender's identity before opening any attachments or providing personal data.
- Regularly refresh your software and operating systems to patch security vulnerabilities.
- Activate multi-factor authentication whenever possible to add an extra layer of security to your accounts.
- Be mindful of the information you share online, and review your privacy settings on social media platforms.
Scrutinize your bank statements and credit card accounts for any suspicious activity. If you notice anything unusual, report your financial institution immediately.
Leveraging Technology to Strengthen Identity Verification Systems
In today's increasingly digital landscape, secure identity verification systems are paramount. As cyber threats evolve and become increasingly complex, leveraging cutting-edge technology is essential for organizations to minimize risks associated with fraud and identity theft.
Multi-factor authentication such as facial recognition, fingerprint scanning, and iris analysis provide a higher level of verification compared to traditional methods like passwords and usernames. By incorporating these technologies into identity verification systems, organizations can bolster their security posture and safeguard sensitive user data.
Furthermore, artificial intelligence (AI) and machine learning (ML) algorithms can evaluate vast amounts of data to detect unusual activity and identify potential fraudulent attempts. These capabilities allow for constant vigilance, enabling organizations to address issues promptly to security threats.
Consistently, embracing technological advancements is crucial for building trustworthy identity verification systems that can effectively combat the evolving landscape of cybercrime.
 Jenna Von Oy Then & Now!
Jenna Von Oy Then & Now!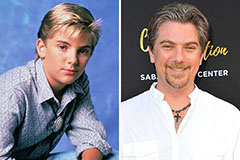 Jeremy Miller Then & Now!
Jeremy Miller Then & Now! Michael C. Maronna Then & Now!
Michael C. Maronna Then & Now! Gia Lopez Then & Now!
Gia Lopez Then & Now! Kerri Strug Then & Now!
Kerri Strug Then & Now!